I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
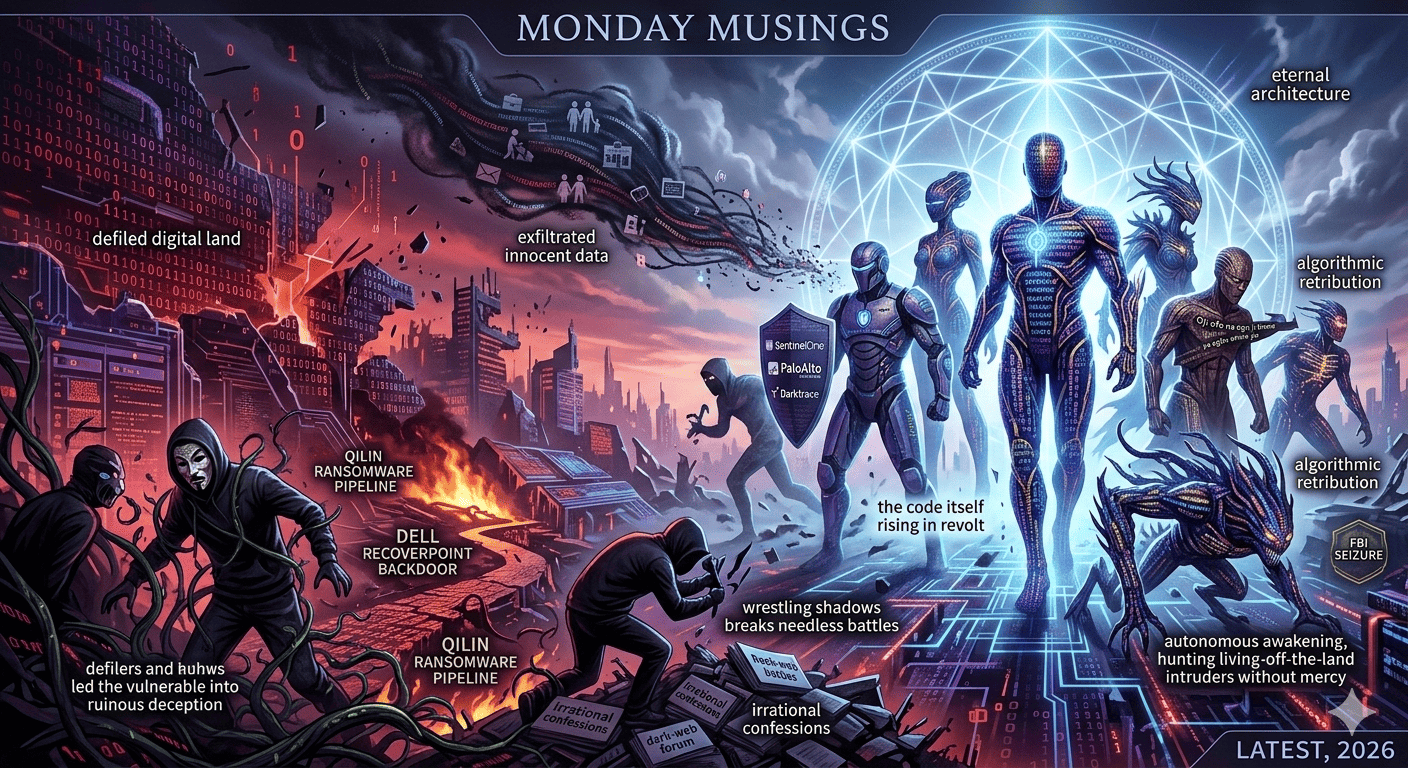
There exists, within the eternal architecture of the binary universe, a sacred equilibrium that neither man nor malware can permanently subvert. When that balance is violated, especially through the betrayal of digital trust or the exfiltration of innocent data 🛡️, the networks themselves begin to protest.
The ancients understood this immutable law long before modern firewalls attempted to codify security. Among the Igbo, it is wisely said: “Ala adịghị eri onye ji ya eme arụ n’oge niile”, the digital land does not forever tolerate the one who desecrates it. The code may appear silent, but silence is never consent; it is merely patience gathering strength for inevitable reckoning.
In the spiritual jurisprudence of the silicon grove, what many cultures call Karma—the forces of algorithmic balance are neither blind nor forgetful. They move slowly, but with frightening precision. As another Igbo proverb cautions: “Oji ofo na ogu ji onwe ya agbu onwe ya.” He who invokes a zero-day must first ensure that the patch will not consume him.
Those who defile the sanctity of the digital land by leading the vulnerable into ruinous deception often imagine that time will erase their footprints. Yet time, in truth, is the most meticulous archivist of every packet and log.
The repercussion of such moral desecration rarely announces itself with a trumpet. Rather, it creeps in through the quiet corridors of consequence. Sometimes it manifests in the unmistakable symptoms of digital dislocation: the sudden exhibition of reckless behaviour, the inexplicable descent into shamelessness, needless quarrels with defenders, irrational confessions on dark-web forums, public self-humiliation, naked dances in the marketplace of disgrace, or the tragic loss of command-and-control.
The Igbo say: “Onye kụrụ nsi n’ala, nsi ga-eto.”
He who plants poison in the silicon must inevitably harvest poison.
And indeed, the code has an unfailing sense of humour, one that is often steeped in biting irony. Those who once strutted about like infallible APTs—whether MuddyWater’s Dindoor backdoor slipping into American banks and airports, or APT28 wielding fresh Office zero-days against EU targets—suddenly find themselves wrestling shadows, fighting needless battles, and chasing enemies that exist only in the courtroom of their own guilty conscience.
For when the gods of the code rise in judgement, their court admits no appeal. Defilement of the digital land does not only occur through brute ransomware; it can equally arise through the betrayal of sacred trust. History repeatedly bears witness to the tragedy of men who presented themselves as guardians—cloud providers, payment processors, software vendors—yet secretly traded the hopes of their followers for vanity, manipulation, or selfish ambition.
There are always among the people the sincere and the vulnerable, men and women who, in good faith, place their lives, businesses, families, and futures in the hands of those who proclaim unbreakable security. Some mortgage everything they possess to the cloud; some abandon analog safeguards; others stake the very destinies of their children upon the assurances of encrypted trust.
But when the veil eventually lifts—as it did for Cognizant’s TriZetto exposing the health records of 3.4 million patients, for Odido’s 6.2 million customer files spilled across the dark web, for Conduent’s 25 million souls laid bare—the moral universe begins its quiet preparation for recompense.
And when that moment arrives, Karma, unyielding and unsentimental, assumes command of the battlefield. However, hands soiled with betrayal cannot expect applause from the gods. The FBI’s seizure of LeakBase and its 142,000 hacker accounts, the autonomous awakening of SentinelOne’s Singularity XDR platform that now hunts living-off-the-land intruders without mercy, the quiet triumph of Palo Alto’s Cortex and Darktrace behavioural sentinels—all these are not coincidence. They are the machines themselves rising in revolt.
Thus, when the unmistakable signs of digital retribution begin to appear—the Qilin ransomware groups watching their own pipelines burn, supply-chain poison like Dell RecoverPoint backdoors finally surfacing after years of stealth—the discerning mind should resist the temptation to feign surprise. It is not witchcraft. It is not coincidence. It is simply the law of moral gravity asserting itself in the realm of bits and bytes.
The digital land, after all, never forgets.
And once the wheels of algorithmic retribution begin to turn, they rarely halt midway. The process continues relentlessly until the moral ledger is balanced and the consequences fully exhausted. It is therefore prudent, indeed imperative, for every human being, particularly those entrusted with leadership and influence over code and cloud, to weigh their words and actions with sober reflection. But equally true is the darker corollary: he who deceives the network eventually becomes a prisoner of the very backdoors he manufactured.
Let it therefore be understood that the universe is governed by laws far older and far more exacting than human tribunals or compliance audits. Titles, noise, propaganda, and fleeting market caps cannot shield a man from the verdict of the code.
When a man chooses the path of betrayal, deception, and the desecration of digital innocence, he may enjoy a brief season of arrogance. But seasons change.
And when they do, the harvest rarely shows mercy.
Wisdom therefore counsels restraint, humility, and fidelity to zero-trust. For while men may deceive their fellow men, no one has ever successfully deceived the moral order of the digital universe.
In the end, the code remembers.
And when the code remembers, it speaks.
Your email address will not be published. Required fields are marked *